Crypto Cards: The New Frontier in Financial Anonymity
Crypto cards: the new border in financial anonymity
The world of cryptocurrency has revolutionized the way we think of financial transactions, allowing peers payments without the need for intermediaries such as banks and governments. However, an often neglected aspect of this new border is the growing importance of financial anonymity. For those who prefer to stay nameless or want to protect their financial activities against prying eyes, cryptographic cards have become a popular solution.
What are the Crypto cards?
A cryptographic card is a digital portfolio designed specifically for cryptocurrency transactions, offering users an additional anonymity and safety layer. Unlike traditional credit / debit cards, which store sensitive information such as account numbers and expiration dates, cryptographic cards do not collect this data. Instead, they use advanced encryption techniques to protect user transactions.
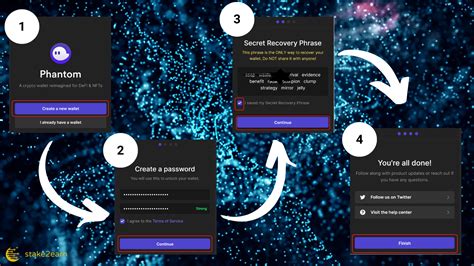
How do cryptographic cards work?
Crypto cards generally consist of a physical card or a digital version, which is linked to an online wallet which contains cryptocurrency funds. When a user performs a transaction using his cryptographic card, the amount is converted into the desired cryptocurrency and transferred directly from the portfolio to the recipient’s address.
The safety features of Crypto cards include:
- Advanced Encryption : Cryptographic cards use advanced encryption algorithms to protect user transactions, ensuring that sensitive information remains secure.
- Zero counts Shart : The online wallet for an cryptographic card never stores sensitive information on the user, which makes it difficult for malicious people to intercept their transactions.
- Decentralized storage
: cryptocurrencies are stored on decentralized networks, reducing dependence on central banks and governments.
Advantages of Crypto cards
The rise of Crypto cards offers several advantages, including:
- Agentation of financial freedom : By providing an additional layer of anonymity, cryptographic cards allow users to carry out transactions without revealing their identity.
- Protection against the regulatory examination : In countries with strict regulations or high levels of government surveillance, cryptographic cards offer a secure alternative to carry out transactions.
- Reduced risk of identity theft : The lack of identifiable personal information (PII) on cryptographic card portfolios makes it more difficult for hackers to target specific individuals.
popular cryptographic map options
Several renowned companies have entered the market with their own ranges of cryptographic cards, in particular:
- Gemini : Gemini is a popular choice among cryptocurrency lovers, offering a secure and friendly interface.
- Bitpay : Bitpay is a well -known company in the payment processing industry, which has developed a range of cryptographic cards that integrate with various wallets and exchanges.
- Coinbase Wallet : Coinbase is one of the greatest exchanges of cryptocurrency, offering its own range of cryptographic cards for users.
Conclusion
Cryptographic cards represent a significant transfer of financial anonymity, offering users an additional layer of protection against regulatory control and identity theft. While the global demand for crypto continues to grow, it is likely that we will see more innovation in this space. For those who appreciate their financial confidentiality and their security, cryptographic cards are really worth it to be considered as a viable alternative to traditional payment methods.
Tips for using cryptographic cards
To maximize the advantages of your cryptographic card:
- Choose a renowned supplier

: Find and select a reliable business with a good reputation.
- Use strong passwords : Always use unique and complex passwords to secure your account.
- Keep your private wallet information : Never share sensitive information about your wallet or personal details.

![Ethereum: Is CPU mining even worth it? [duplicate]](https://kitchenwireproducts.com/wp-content/uploads/2025/02/a15f028b.png)