Vesting Period, Mempool, Price Volatility
“Crypto periods: Impact on prices volatility and pool use”
The crypt market is known for its high pricing volatility, with prices rapidly and unpredictably fluctuates within hours or days. One of the key factors that contribute to this volatility is the cryptomen claim.
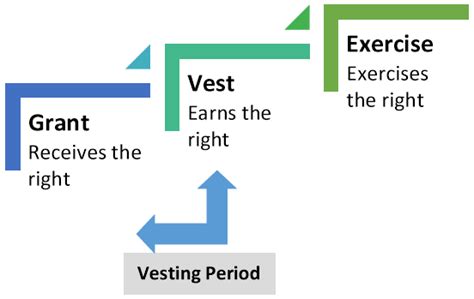
What is the period of handing over?
The entitlement period is a time frame during which the cryptocurrency owner must hold his coins before they can be moved or sold. This means that as soon as the user holds a certain percentage of his crypto, part of it will be automatically unlocked and released over time.
How does it affect the price management period of the price?
The period of entitlement has a significant impact on the volatility of prices in the crypt market. When a user reports a large number of coins, this can lead to an increase in demand for these specific cryptomises. This increased demand may increase prices, causing market volatility.
For example, if the user owns 10% of his bitcoin and then reports an additional 5%, now owns 15% of this cryptocurrency. If the price of bitcoin increases significantly during this time, the percentage of ownership of the holder will increase, increasing the price of the entire coin.
MEMPOOL: centralized pool for crypto transactions
Another factor that contributes to the volatility of prices is a mempool, a centralized group of transactions that allows users to buy and sell cryptocurrencies. MEMPOOL uses many popular exchanges such as Binance and Kraken, and is accessible to their websites or mobile applications.
MEMPOOL volatility and prices: double -edged sword
While a mempool can facilitate fast and low fees for users, it also creates a centralized platform that can be misused by harmful actors. If a large number of users hold coins in the same pool, they can create an “price bubble” effect where prices are rising rapidly when more users are connected.
This is known as a “mempool effect” and has been observed in various cryptomes, including bitcoins and ethereum. Fast price overvoltages caused by a mempool may be harmful to users who have already granted their coins or held a small part of their total shares.
Volatility MEMPOOL Prices: Call for Regulation
The extensive use of the mempool has caused concern about its impact on cryptoms. Some experts say that a mempool should be regulated closer, as it can create an environment leading to the price handling and volatility of the market.
To alleviate this risk, regulatory authorities require increased supervision of centralized exchanges such as Binance and Kraken. This includes stricter laundry regulations against dirty (AML) and know-you-cusomer (KYC), as well as increased requirements for mempool reports.
Conclusion
In conclusion, the periods of authorization, mempool and volatility of prices are all interconnected factors that can affect the crypt market. While the mempool can facilitate fast and low fees, it also creates a centralized platform that can be misused by harmful actors.
MEMPOOL’s regulation has been invited to alleviate its risks, but more work needs to be done to ensure that cryptocurrency markets remain safe and safe for users around the world.
References
- “Claim Period: Key Factor of Volatility Cryptocurrency” (cryptoslate)
- “Mempool Effect: Two -edged sword on crypt markets” (Coindesk)
- “Regulation of centralized exchanges to mitigate the risks of mempool” (Binance Blog)